The Machine Behind The Multipolar Myth
Why the Control Grid Has No Flag and How to Exit It
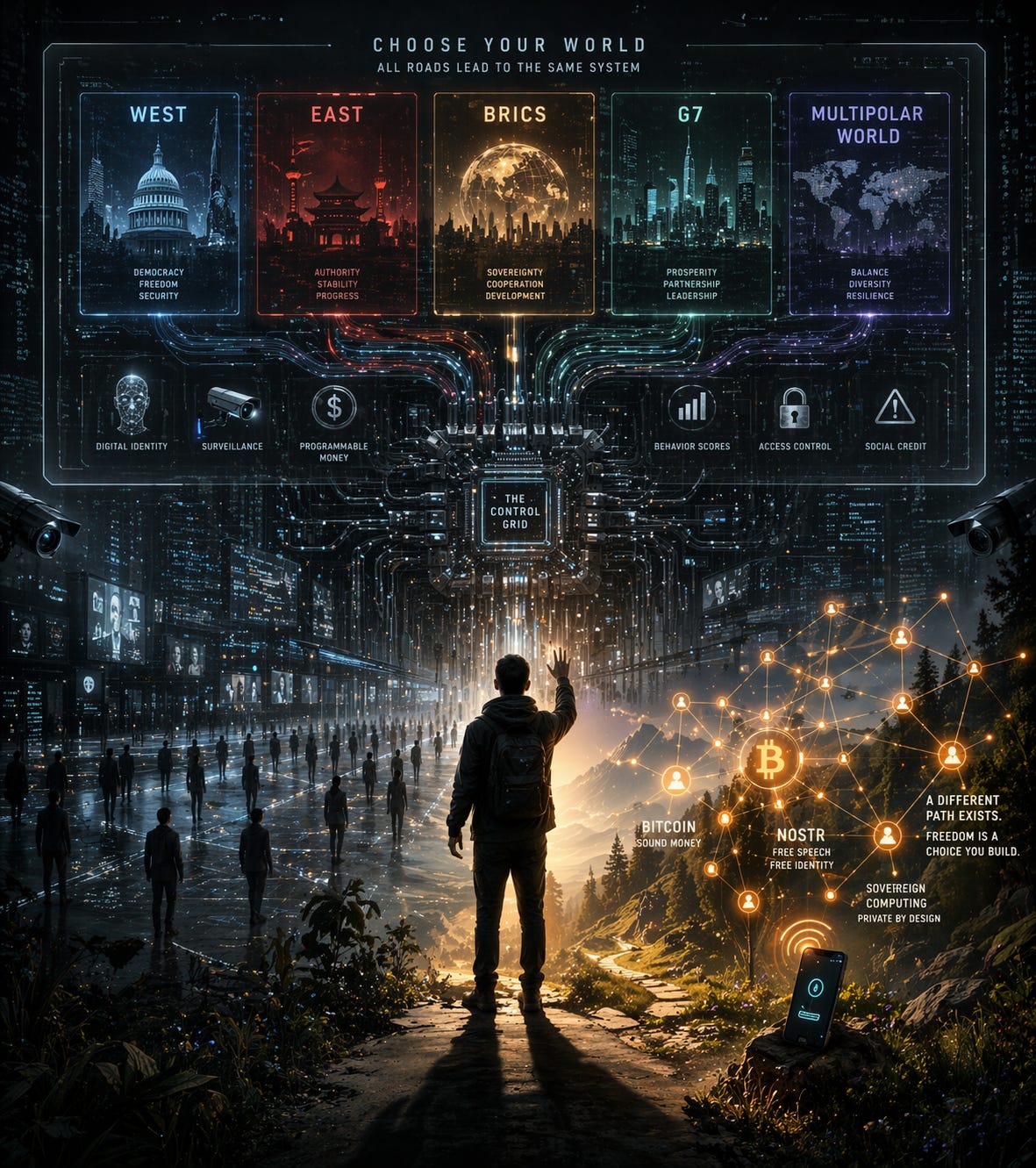
There is a narrative that has been doing the rounds for a long time, especially since the Russia-Ukraine conflict broke out. It goes something like this; the American-led unipolar world, rules based order is collapsing, along with its imperialistic institutions like IMF and World Bank; and is being replaced by a fairer and more just multipolar world led by the BRICS countries. In this multi-polar world, dollar hegemony is going to give way to either gold as the reserve currency or a basket of currencies, while at the same time ensuring national sovereignty of even weaker but resource rich nations in the global south that were victims of the US empire. The old world order is certainly cracking right? Wrong. If anything this is one of the most consequential misdirections of our time.
There is a fundamental question that remains conspicuously absent from the current discourse, which is, what is the actual architecture being erected on the far side of this transition? If one strips away the superficial branding; East versus West, BRICS versus the G7, or the facade of multipolarity against hegemony and scrutinizes the technical infrastructure being deployed across every major nation in lockstep, a far more sobering picture emerges. You immediately realize that this is not a collision of rival systems designed to restrain power; but it is a synchronized convergence of systems achieving its final apotheosis. Identical digital identity protocols, programmable currency frameworks, and pervasive surveillance infrastructures are being built and gradually integrated in lockstep, and this machine is signaling a world in which every individual’s identity is state-verified, every transaction is state-visible, and access to both can be unilaterally revoked at will.
The question of which bloc wins the multipolar struggle is, in this light, a question about management succession. In other words a multipolar world isn’t a counterpoint to centralized power but a bitter rivalry between competing factions who are bidding for control of the aforementioned machine. The multipolar world does not threaten this architecture but accelerates it, by giving each pole the political cover to implement at home what it condemns abroad, and by driving every state toward the same surveillance infrastructure under the competitive logic of national security. Therefore the argument that this is a “multipolar world order” where different civilisational blocs pursue genuinely different visions of human organisation is not supported by what is actually being built.
What is being built, on both sides, is a technocratic governance architecture in which all economic activity requires identity verification, all transactions are visible and tracked, programmable conditions can restrict or block specific purchases or movements, and compliance with “international standards” is the price of access to the system. The standards themselves (e.g. Basel rules, SDG indicator) are largely set by institutions like the World Economic Forum (WEF) and UN that are not elected by anyone and are not accountable to the populations that will live under the systems they design.
For example, Iran, Russia, and China are presented as the unjust victims and therefore opponents of the Western-backed system but are they offering a different vision for the world that puts the individual citizen at the centre by reducing the influence and power of the state over his life? Emphatically no! All three are members of the fiat money cartel given that they all have central banks that print money ad infinitum, they all enforced Covid lockdowns in step with the rest of the world, they all formally support the UN Sustainable Development Goals, they are all building digital identity infrastructure and they are all actively developing central bank digital currencies (CBDCs).
This essay is about that machine; who is building it, how coordination happens across nominal political divides, and why the only coherent response is neither a political movement, nor an electoral coalition, but a technical counter-architecture; a sovereignty stack built on Bitcoin, organised into non-aligned communities that sovereign individuals can inhabit.
The Digital Cage: Russia as Proof of Concept
To understand what the control grid looks like when fully operational, begin not with China whose system, though architecturally advanced, is more fragmented than Western press coverage suggests, but with Russia. Gosuslugi, Russia’s digital public services portal, was once a mundane convenience: pay parking fees, schedule a passport appointment, enroll your child in school. In 2023, it became something categorically different. Under legislation passed that year, a military conscription summons is now considered legally delivered the moment it appears in a citizen’s Gosuslugi account or, for those without an active account, seven days after it is entered into the Unified Register of Conscripts. No physical delivery required.
Once the summons have been issued, the consequences kick in immediately. A travel ban activates immediately upon delivery, before the 20-day response window even begins. If the conscript fails to report within those 20 days, the system triggers further restrictions: the driver’s licence becomes invalid in the traffic police database; the land registry blocks any property transactions; banks see a conscription restriction flag and deny loan access; self-employment registration is blocked. The state has, without any judicial proceeding, suspended the citizen’s effective economic existence.
When Russians began attempting to delete their Gosuslugi accounts in March 2023, the authorities disabled the delete-account function on the same day the Defence Ministry announced the electronic summons system. The system is also integrated with a network of over 200,000 facial-recognition cameras in Moscow. Conscripts who contested their draft orders in court found themselves entered into a state database as alleged evaders, triggering facial recognition alerts that enabled police to detain them on the spot, not for any proven violation, but for the act of legal contestation itself.
This is not a war emergency measure that will be reversed after the emergency passes, but seems more like the justification for merging all databases; tax, police, medical, military — into a single operational control system. Russia has demonstrated something important to every government watching: a digital public services portal, once sufficiently embedded in daily civic life, can be converted into a mechanism of coercive enforcement with a legislative change and a few software updates. That’s notwithstanding the fact that Gosuslugi is tightly integrated with the digital ruble (the Russian CBDC), primarily through identification and access control. What this means is that without Gosuslugi authentication, you cannot access or use the digital ruble platform. Gosuslugi does not host the digital ruble wallet itself, but it serves as the mandatory digital identity gatekeeper for the entire system. This is consistent with Russia’s strategy of centralizing identity and surveillance through Gosuslugi.
Curated Rivalry, Shared Plumbing
The West watches Russia’s Gosuslugi apparatus with the comfortable assumption that such things happen elsewhere, in authoritarian states, not here. This comfort will be short-lived as the architecture being built in liberal democracies is not opposed to Russia’s model. It is the same model, running on a different political timeline.
Brussels based Swiss author, Jacques Baud, who is also a former colonel and intelligence analyst; was added by the EU to its sanctions list for “acting as a mouthpiece for pro-Russian propaganda and making conspiracy theories…implementing or supporting actions or policies attributable to the Government of the Russian Federation which undermine or threaten stability or security in a third country (Ukraine) by engaging in the use of information manipulation and interference.” A long winded way of saying he was critical of the west’s handling of the Russia-Ukraine conflict.
Despite there not being any evidence presented of him being an agent funded by the Kremlin, Baud has been banned from travelling within the EU/Schengen Area, all of his bank accounts have been frozen and his friends or family are prohibited from assisting him financially or with provisions. He can’t even return home to Switzerland. All of this happened without trial or even formal allegations of a criminal offense; this was all done by decree.
As far as irony goes this incident is full of it. The EU, while posturing as the moral guardian of human rights against the Kremlin, employs the same mechanism of summary decree to erase a citizen’s existence. Mind you, this is happening before the full implementation of the digital control grid. The most important question of all therefore is this; is the censorship infrastructure in Brussels different from that in Moscow? If not, then the individual is left without a sanctuary in either jurisdiction.
As of 2025, approximately 134 countries and currency unions, representing roughly 98% of global GDP, are at some stage of developing a Central Bank Digital Currency. This figure includes China, Russia, the European Union, India, Brazil, Saudi Arabia, Nigeria, and virtually every economy of consequence. The e-CNY is in active deployment across dozens of Chinese cities, the digital euro is in its preparation phase, while Russia’s digital ruble has cleared the pilot stage. The Bank for International Settlements, whose member representatives from nominally adversarial nations meet monthly regardless of whether their governments are currently sanctioning each other, has been the intellectual and technical architect of much of this convergence. Its Innovation Hub actively develops CBDC interoperability standards, the technical specifications that will determine whether programmable money can be frozen, redirected, or conditioned on compliance across jurisdictions.
For example, Project mBridge links central bank digital currencies across China, Hong Kong, Thailand, the UAE, and Saudi Arabia. Its research papers openly describe the programmability of CBDC as a feature, not a warning.The key word is interoperable. The e-CNY and the digital euro need not look alike. They need only settle with each other, trace each other’s transactions, and enforce each other’s sanctions lists. While the visible layer may be national, the control layer is shared.
The Financial Stability Board coordinates financial regulation across the entire supposed multipolar divide. The IMF extends conditionality that consistently favours the same financial architecture regardless of which bloc a borrowing nation nominally aligns with. This technocratic order is a network of interlocking institutions, standards bodies, public-private partnerships, and treaty frameworks that effectively govern the conditions of human life without being accountable to any democratic constituency. The BIS sets monetary standards. The ITU sets telecommunications standards. The WHO sets health emergency protocols. The WEF convenes the public-private partnerships that implement all three. These institutions are not elected and they cannot be meaningfully voted out.
This is the core deceit of the multipolar narrative. BRICS nations are not challenging the control grid, but they are demanding their seat at the table that operates it. Russia is not building an alternative to SWIFT because it opposes financial surveillance; it opposes being on the wrong end of it. China’s challenge to dollar hegemony is not a challenge to monetary control; it is a bid to relocate the centre of that control. The result, in every scenario where this competition plays out through existing institutions, is a world divided into surveillance jurisdictions rather than a world in which surveillance is abolished.
The individual; the citizen, the entrepreneur, the dissident, the ordinary person trying to live a life of their choosing, has no constituency in this competition. Both sides want your identity registered, your money programmable, your communications monitored, and your behaviour scored. They simply disagree about who should do it.
The Protocol That Has No CEO
The architecture described above is not, at its core, military or even political. It is a metabolic apparatus that controls access to economic life the way a body controls access to nutrients; through a system of gates, each of which requires identification, each of which can be closed. The biometric digital ID is not the ID of a citizen; it is the key to the gate in the same way that the CBDC is not money but a programmable permission slip. Agustín Carstens, the General Manager of the BIS, articulated the end goal plainly when he said: “Central banks will have absolute control on the rules, and will have the technology to enforce that.” This architecture does not need soldiers at checkpoints. It needs only that every economic participant be visible, identifiable, and therefore conditionable.
Against this machine, political resistance is necessary but insufficient. Every political movement that has fought the control grid through electoral politics has discovered the same thing; which is that the infrastructure persists across governments. The surveillance apparatus does not change hands or stop when parties change. The CBDC framework, once enacted, will not depend on which coalition controls the parliament. Donald Trump did not end the NSA’s surveillance programs. Brexit did not liberate Britain from the EU’s digital identity framework but it simply moved the UK into a position of regulatory price-taking with respect to standards it no longer helps to set. The control grid is not a policy, but it’s a technical and institutional infrastructure that also requires a technical and institutional counter.
That counter exists but it’s incomplete, not yet operating at full scale, and facing sustained institutional opposition. Its architecture is sound, and its underlying logic is more robust than any political coalition because it does not depend on winning any election. I call it the sovereignty stack. This sovereignty stack must therefore operate on a single foundational premise: illegibility. A participant who cannot be identified cannot have their transactions conditionally blocked, communication that passes through no central server cannot be seized at source. A monetary unit whose supply rule is enforced by mathematics rather than by an institution cannot be debased to fund wars whose financial positions were taken before the bombs fell.
Layer one: sound money
The state does not create money. It captures money, monopolises its issuance, and then degrades it through inflation to finance its own projects without the political pain of visible taxation. The CBDC is the completion of this process. Physical cash still permitted residual illegibility; a transaction in banknotes left no trace in any database. The CBDC eliminates that residual entirely.
Bitcoin is the only existing monetary instrument that is structurally immune to this. The network has processed transactions continuously since January 2009, through coordinated narratives of criminality, through the Chinese mining ban, through the ETF-ification of its investment exposure. The protocol has never been compromised and there is no transaction that can be blocked because the sender or receiver has been designated an enemy of the state. Bitcoin is bearer money: if you hold the keys, you hold the money, and no entity in the world can confiscate it without your cooperation. Every sanctioned state should be on a Bitcoin standard by now but the only reason why they are not is that despite the political squabbles that we see on the surface; they won’t adopt Bitcoin fully because they still want to retain the power to print money.
Layer two: decentralized communications
Identity verification, transaction monitoring, and programmable conditions all require communication channels. The control layer is a communications layer. Censoring a payment and censoring a message are the same technical operation, both require that the communication pass through a node that the controller owns.
The existing internet was not designed for surveillance, but it was not designed against it. Platforms are centralised by their architecture; Twitter, Facebook, Gmail, and WhatsApp all depend on servers that can be subpoenaed and seized. Nostr is the communication and identity layer
Nostr (Notes and Other Stuff Transmitted by Relays) is a protocol, not a platform. Its design is the minimum necessary structure for censorship-resistant communication where users hold cryptographic keypairs, sign their messages, and broadcast to any relays willing to receive them. There is no central server to seize and there is no company to subpoena. There is also no account to deactivate since a user’s identity is their public key, derived mathematically from their private key, which never leaves their own device. There is also no KYC process that gates access. Furthermore, Nostr-native marketplaces for goods, services, real estate, and professional contracting are being built on these primitives now, using Bitcoin for settlement and cryptographic reputation for trust.
Layer three: sovereign computing
The weakest point in any sovereignty stack is the device. A cryptographic keypair is theoretically unbreakable; a device whose operating system reports its activity to a cloud service is not. GrapheneOS completes the stack at the device layer. GrapheneOS is a hardened Android fork with a security model designed from the assumption that the user is the threat model’s subject, not its operator.
A standard smartphone running Android or iOS is, by design, a surveillance endpoint: it reports location, contacts, application usage, and communications to corporate intermediaries who are subject to state demands. GrapheneOS eliminates this attack surface; no Google Play Services, no persistent cloud telemetry, hardware-enforced application sandboxing. Paired with local AI inference running open-source models on-device, it enables a computing environment in which the user’s data and cognitive work remain private not by policy but by architecture. Network permissions are granular and revocable per application. The attack surface for remote exploitation is systematically reduced. Multiple isolated profiles allow a user to maintain entirely separate digital identities on a single device (e.g. a merchant profile, a personal profile, a communications profile) with no data leakage between them.
The device is the sovereignty boundary. The key to a Bitcoin wallet is worthless if the device that holds it is compromised, just as the Nostr identity is worthless if the application that signs messages reports its activity to a third party. The sovereignty stack does not become sovereign at the protocol layer. It becomes sovereign at the point where the private key is generated and stored, which is the device. GrapheneOS makes the device the user’s property in a functional rather than merely legal sense.
Layer four: the Hanseatic model
Architecture alone is not enough. The sovereignty stack is a set of tools, but what matters is the social form in which those tools are used. Philippe Dollinger‘s comprehensive history of the German Hansa documents an economic alliance that, between the twelfth and seventeenth centuries, controlled the trade of the northern European world without a state, without a central bank, without a standing army of significance, and without anything resembling the regulatory apparatus that modern commerce is assumed to require. The Hansa was a league of merchant cities. Its governance was the Hansetag, a periodic assembly of representatives who set the terms of mutual recognition and common standards by consent, not by hierarchy. Its enforcement mechanism was the boycott; the withdrawal of commercial relationships from those who violated the terms of membership, an economic sanction that required no violence and no state apparatus to administer. In short, the Hansa was a voluntary network of trading communities, which at its peak, had over 200 cities and posts from London to Novgorod, bound by shared commercial law, mutual recognition, and the practical interest in maintaining open trade routes. The Hansa did not request permission from feudal lords to trade across their territories. It built the infrastructure that made those borders economically irrelevant to its members.
A Hanseatic merchant in Lübeck could arrive in Riga, Bruges, or Bergen knowing that the other Hanseatic merchants there would honour his bills, provide storage and insurance, extend credit, and enforce agreed contract terms. This was not altruism but the rational recognition that participation in the network was worth more than defection from it. The network’s standards were not imposed by a sovereign, but they were voluntarily adopted by merchants because adopting them increased the value of their membership.
This is the governance model that the sovereignty stack’s market layer requires. The Bitcoin circular economy works at the level of individual peer-to-peer transactions. What extends it to a genuine alternative economic network is the Hanseatic structure: communities of merchants who accept bitcoin and extend mutual recognition to each other’s contracts and credit. The kontor (the Hanseatic trading post) was not a branch office of a central company. It was a node in a network, applying common standards locally, governed by the merchants who used it.
The structural parallel to our present moment is precise. The question is not how to overthrow the control grid but it is how to build an alternative so functional, so economically productive, and so deeply embedded in the lives of its participants that the control grid becomes a system people choose to leave rather than a system they are forced into.
The stack as a whole
Each layer defeats a specific component of the control architecture:
Bitcoin defeats the CBDC at the monetary layer
Nostr defeats identity-verification at the communications layer
GrapheneOS defeats device-level surveillance at the hardware boundary
The Hanseatic circular economy defeats conditional access at the market layer
The critical insight is that the stack must be in place before the dependency is created. A population that already holds bitcoin, already communicates over Nostr, already operates sovereign devices, and already participates in a Hanseatic circular economy cannot be made dependent on the machine economy’s conditional access, because it has an alternative. A population that has first been made dependent has no alternative, because the alternative was never built. This is the race that the sovereignty stack describes. It is not a race between states or between blocs. It is a race between two incompatible architectures for organising economic life, being built simultaneously, in the same territories, for the same populations.
The control grid is being built by institutions that span the supposed geopolitical divide, share standards while wearing different flags, and use crisis as a parameter update and convenience as a sedative. It is being built toward a single destination: from anonymous to identified, from cash to CBDCs, and from natural law to algorithmic enforcement. The great political question of the 20th century was about who should control the state. The great political question of the 21st century is whether the technocratic network that has grown up around and above the state should be the primary organising institution of human life at all.
The sovereignty stack does not answer that question by winning an argument. It answers it by building something. It gives individuals and communities the tools to demonstrate through practice;not through manifestos, not through elections, that human beings can organise their economic and social lives without the permission of states, platforms, or the governance networks that coordinate above them.
The most powerful form of civil disobedience is not protest but the creation of conditions in which unjust authority simply cannot reach you. The Bitcoin network is that condition for money, Nostr is that condition for speech and identity and sovereign computing is that condition for thought. Together, they are the infrastructure of a life that does not require the state’s permission to be lived.


You might want to add "Attestation" to the stack for sovereign computing. Essentially it's hardware level support for creating hashes of virtual machines that are guaranteed to be running what matches the signed hash. In short as long as the signature matches the virtual machine you rented from the cloud ran exactly only your code.
Smart phones are great but we need to leverage more substantial compute than that to be relays etc for p2p architecture. I don't want to setup a server rack in my guest bedroom.